Our Blog
-

Retail-Ready IT: Designing a Secure, Scalable Network Without Enterprise Waste
Opening a retail business today requires more than shelving products and setting up a register. Modern retailers depend on reliable connectivity for email marketing, e-commerce, credit card processing, vendor coordination, and real-time communication with customers and suppliers. The challenge is building a network architecture that delivers enterprise-grade capability without enterprise-level cost. The objective is not
-

Protection of Private Information in a Data-Driven World
In today’s technological environment, privacy and convenience exist in constant tension. Organizations collect personal data to automate processes, anticipate user needs, and deliver services that feel seamless and intelligent, yet that same data collection can quickly drift into surveillance or misuse when boundaries are unclear. This tradeoff is not abstract. It unfolds each time a
-
The Architecture Behind the Experience: Why Network Design Defines Customer Trust
Modern organizations communicate with customers through a layered mix of digital channels. Email remains the backbone for billing notifications, policy updates, and scheduled maintenance alerts. SMS messaging provides near real time communication during outages or appointment windows. Web based chat tools and automated phone systems offer status updates, estimated wait times, and self service options.
-
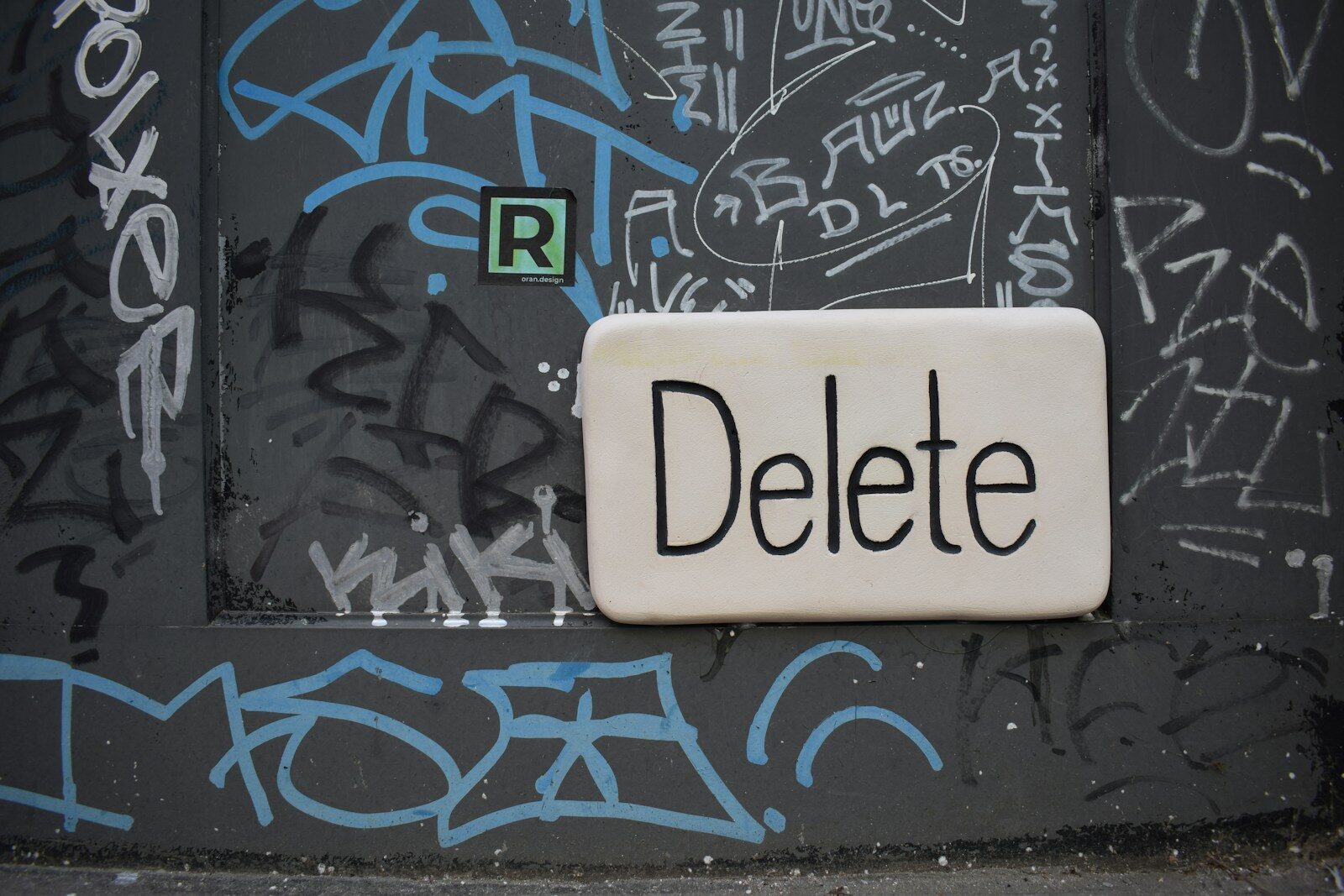
Speech, Platforms, and Power: Rethinking Censorship in the Digital Public Square
When people debate censorship on the internet, the conversation often starts with the image of governments banning ideas outright. In practice, the modern dispute is less about prohibiting individual viewpoints and more about how platforms design, amplify, and manage content at scale. A recent example is the European Commission’s enforcement action against X under the
-
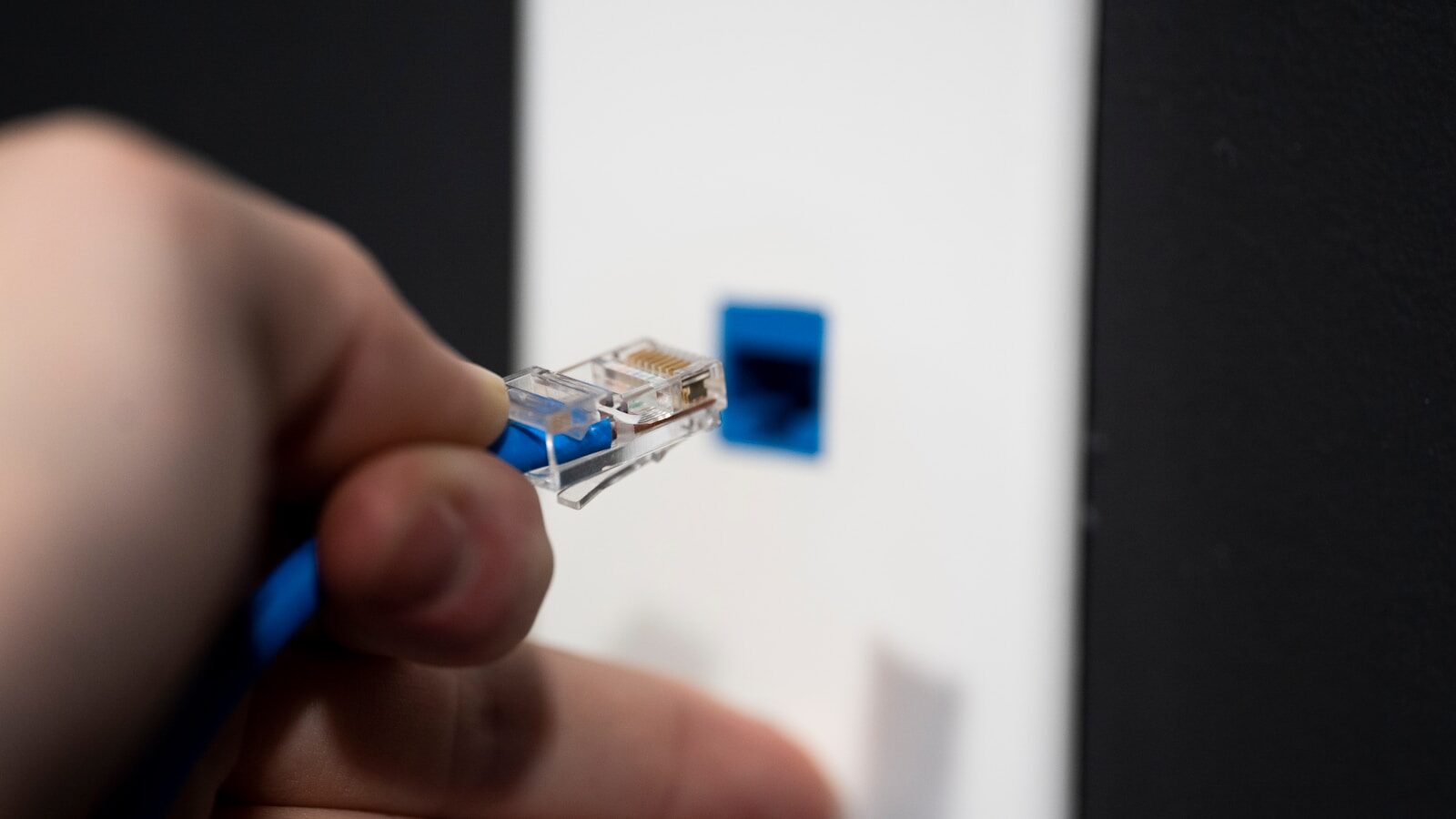
Routing the Invisible Highway: Why Layer 3 Still Runs the Modern Enterprise
The OSI model is often introduced as an academic framework, a seven-layer vertical stack that organizes the complex task of inter-networking into discrete, logical functions. In practice, it is far more than a diagram in a textbook. It is a strategic lens for understanding how modern enterprises move information securely and reliably across increasingly distributed
-

When Privacy Is Breached in the Digital Age: Why Tort Law Still Matters
Tort law remains one of the most practical and adaptable tools for protecting privacy in a world where personal information moves faster than ever and reputational harm can scale globally in minutes. At its core, tort law provides civil remedies when an individual’s personal information, reputation, or emotional well-being is harmed, and traditional privacy torts
-

Securing the Backbone: Why Security and Scalability Define Modern Government Networks
The modern public sector operates on an invisible backbone that is as critical as any highway or power grid: its network infrastructure. From processing identification records and managing benefits to coordinating emergency response and public communications, government operations now depend on digital systems that must be continuously available, resilient under pressure, and secure by design.
-

Security in the Age of Relentless Cybercrime
Computer crime is no longer a niche technical concern; it is the primary force shaping modern information security strategy. Early IT environments operated on the assumption that networks had clear perimeters and that threats were limited and identifiable. That worldview has collapsed. Today’s adversaries operate across borders, automate their attacks, and exploit both software vulnerabilities
-

The Future They Imagined
There is something oddly charming about a bunch of Americans in 1998, tethered to their kitchen walls by landline cords, being asked to imagine the year 2025. The CNN piece digging up this Gallup and USA Today poll feels like opening a time capsule and realizing the past was both smarter and more naive than
-

E-Commerce, Clicks, and the Fine Art of Agreeing to Things Online
E-commerce sits at an interesting crossroads between old legal ideas and very modern behavior. Common law, built through judicial decisions and precedent, evolves slowly and tends to adapt principles over time. Contract law, on the other hand, provides more explicit rules about how agreements are formed, what counts as assent, and when an obligation becomes
